Most organizations expect attacks at the application or endpoint level. Fewer are prepared for abuse that lives inside the network itself.
Today’s attackers rely on infrastructure. They abuse IP space, hosting platforms, DNS, and email networks to scale fast and disappear quickly. If you only focus on endpoints, you miss where most large-scale attacks actually begin.
Understanding the most common network security threats and abuses helps teams move from reactive cleanup to real prevention.
What we mean by network security threats and abuse
Network security threats and abuses involve the misuse of internet infrastructure to deliver attacks, move laterally, or enable fraud at scale.
Instead of targeting a single system, these threats exploit:
- Shared networks and IP ranges
- Hosting and cloud resources
- Protocols like DNS and SMTP
- Weak abuse handling processes
The result is widespread impact with relatively little effort from attackers.
The most common network security threats to prepare for
Spam and bulk email abuse
Spam is still the most common abuse signal on the internet. It is also the foundation for more serious attacks.
Modern spam campaigns are used to:
Unchecked outbound spam quickly damages network reputation and leads to blacklisting.
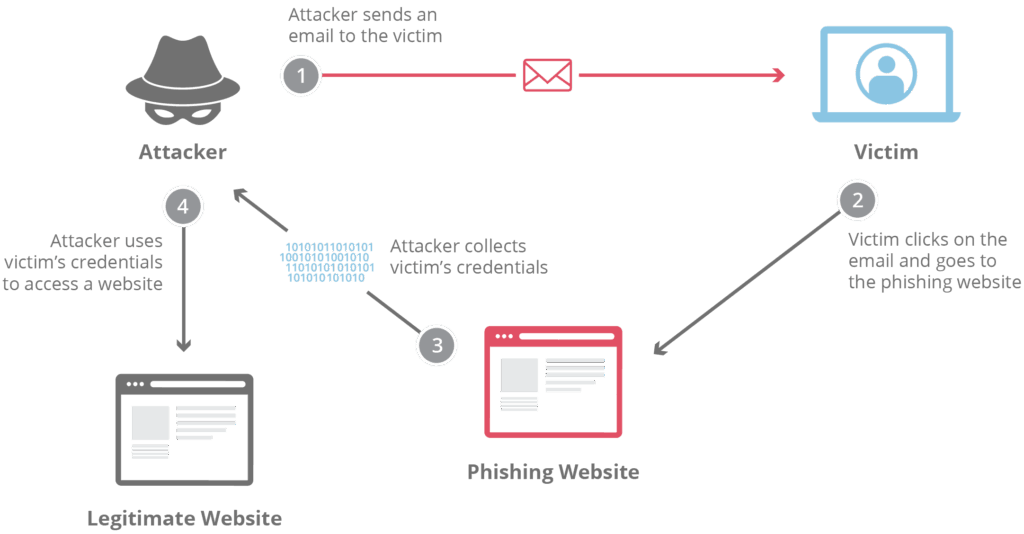
Phishing infrastructure
Phishing is no longer just about emails. Attackers spin up short-lived hosting to run fake login pages, brand impersonation sites, and credential harvesters.
These sites often move every few hours, which makes slow detection ineffective. Network-level visibility is critical to stop them early.
Malware hosting and distribution
Many networks unknowingly host:
- Malware download servers
- Payload staging systems
- Update endpoints for infected devices
Even brief exposure can result in thousands of downstream infections.
Botnets and automated abuse
Botnets turn compromised devices and servers into large-scale attack tools.
They are commonly used for:
Botnets rely on constantly rotating infrastructure, which allows them to survive weak response processes.
DDoS attacks and amplification abuse
Distributed denial-of-service attacks overwhelm networks by abusing bandwidth and protocol behavior.
Some attacks rely on:
- Compromised servers as launch points
- Misconfigured services as amplifiers
- Large botnets generating traffic floods
Preparation requires visibility into traffic patterns, not just firewalls.
Command-and-control infrastructure
Malware needs a way to receive instructions. That is where command-and-control infrastructure comes in.
These systems often hide in plain sight on legitimate hosting and cloud platforms, using DNS and HTTPS to blend in with normal traffic.
Scam and fraud hosting
Investment scams, fake stores, and impersonation sites depend on hosting providers that fail to act quickly.
Fraud infrastructure is designed to:
- Appear legitimate
- Rotate domains and IPs rapidly
- Exploit slow abuse handling
This creates real-world financial harm and regulatory risk.
Compromised customer accounts
Not all abuse comes from attackers creating new infrastructure. Many incidents involve legitimate customer accounts that have been compromised.
Signs include:
- Sudden traffic spikes
- Abnormal outbound email behavior
- Repeated abuse complaints
If not caught early, these accounts become repeat offenders.
Why these threats persist
Abuse lives upstream
Most large-scale abuse originates from ISP, cloud, and hosting subscriber networks. If the source network does not act, the abuse continues.
Reporting is inconsistent
Many organizations block attacks locally but never report them back to the originating network. That breaks the remediation loop.
Manual processes do not scale
Abuse desks are overwhelmed. Without automation, response times stretch from minutes to days.
Attackers only need hours.
Reputation damage spreads fast
Once a network develops a poor reputation, even clean customers suffer. Deliverability drops, access is restricted, and trust erodes.
Where these threats cause the most damage
Network abuse leads to:
- Blacklisted IP ranges and domains
- Increased operational and support costs
- Customer churn and brand damage
- Regulatory and compliance exposure
For infrastructure providers, these are business risks, not just technical ones.
How to prepare for network-level threats
A practical defense-in-depth approach includes:
- Continuous monitoring of network and protocol behavior
- Early detection using threat intelligence and reputation data
- Fast reporting back to originating networks
- Automated abuse handling to reduce response time
- Clear documentation for audits and compliance
Frameworks such as the NIST Cybersecurity Framework emphasize detection and response. Network visibility is essential to meeting those expectations.
Tools and intelligence that help
Threat intelligence feeds that focus on infrastructure, not just malware samples, provide early warning signals.
Platforms like Abusix Guardian Intel help teams understand:
- Where abuse is originating
- How infrastructure is reused
- Which networks pose recurring risk
When paired with automated abuse management, these insights turn into faster takedowns and cleaner networks.
Common mistakes that keep networks exposed
- Treating abuse as a ticket queue instead of a security signal
- Ignoring outbound traffic behavior
- Blocking locally without reporting upstream
- Relying only on endpoint security
Each mistake extends the life of abuse campaigns.
Preparation starts at the network
The most common network security threats are not exotic. They are persistent, infrastructure-driven, and highly automated.
Organizations that prepare for them focus less on chasing individual incidents and more on controlling how their networks are used.
If you want better visibility into network abuse and practical ways to respond faster, visit https://www.abusix.com/contact-us to continue the conversation.
FAQ
What is the most common network security threat today?
Spam remains the most common signal, but it often supports phishing, malware, and fraud.
Why are hosting and cloud providers frequent targets?
They offer scalable infrastructure that attackers can abuse if monitoring and response are slow.
Are DDoS attacks still a major concern?
Yes. DDoS attacks continue to evolve and often rely on abused infrastructure rather than raw bandwidth alone.
How does network abuse affect compliance?
Unresolved abuse can signal lack of due diligence, which creates regulatory and audit risk.
Can automation really reduce network abuse?
Yes. Automation shortens response time and limits how long attackers can operate.