DNS queries are happening whether you notice them or not
Every time someone visits a website, sends an email, or opens an app, DNS is involved. DNS queries are one of the most fundamental signals on the internet, yet they are often misunderstood or oversimplified.
For network operators, hosting providers, and security teams, DNS query data is more than background noise. It is a rich source of insight into traffic patterns, performance issues, and abuse activity. Understanding what DNS queries are and how they are measured helps make sense of what is really happening on your network.
What is a DNS query?
A DNS query is a request sent by a device asking for information about a domain name.
In plain terms, it answers questions like:
- What IP address belongs to
example.com? - Which mail server handles email for this domain?
- Does this domain even exist?
A simple example:
When you type www.example.com into a browser, your device sends a DNS query asking for the IP address so it knows where to connect.
The basic types of DNS queries
Not all DNS queries are the same. The most common types include:
- A and AAAA queries
- MX queries
These identify mail servers responsible for handling email.
- NS queries
These ask which name servers are authoritative for a domain.
- TXT queries
Often used for verification, email authentication, and security policies.
Each query type serves a different purpose, but all follow the same basic resolution process.
How DNS query resolution works
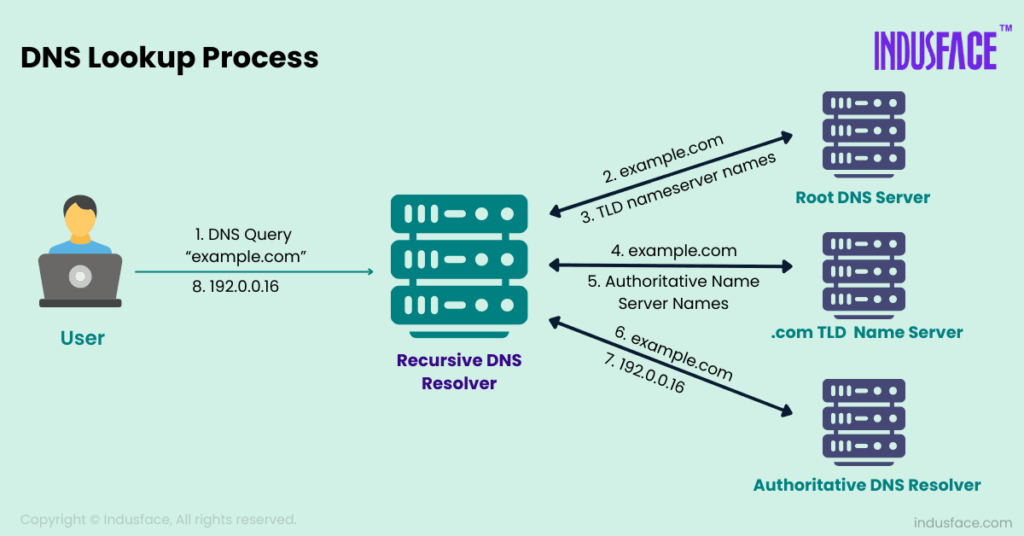
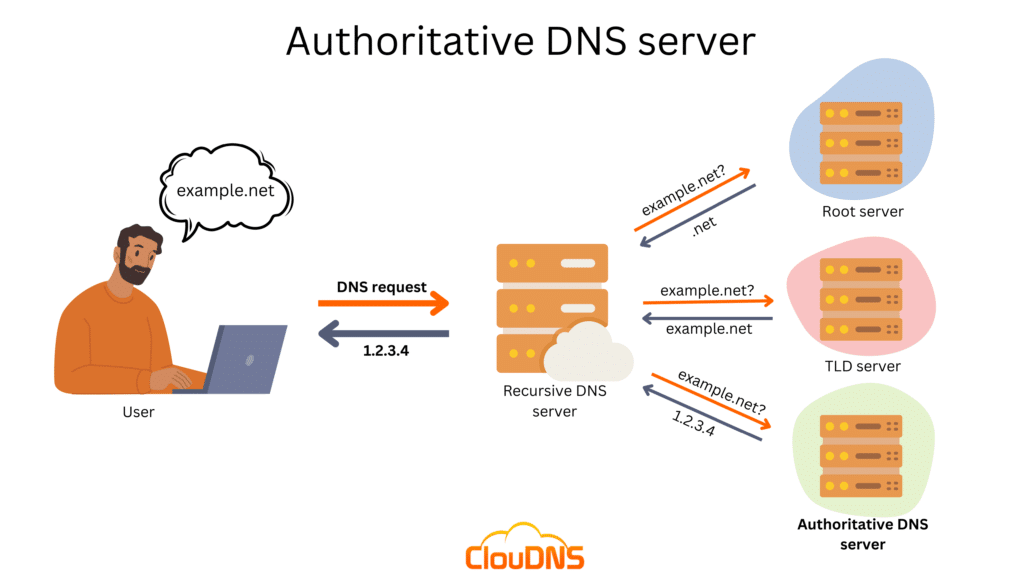
When a DNS query is made, it usually follows this path:
- The user’s device sends a query to a recursive resolver
- If the answer is cached, the resolver responds immediately
- If not, the resolver queries authoritative name servers
- The final answer is returned to the user
This entire exchange often happens in milliseconds.
Organizations like ICANN coordinate the global DNS ecosystem, while large providers such as Cloudflare and Google operate widely used recursive resolvers.
What DNS queries can reveal
DNS traffic is lightweight but highly informative. At scale, DNS queries can show:
- Which domains users are trying to reach
- How frequently domains are accessed
- Sudden spikes in lookups for new or suspicious domains
- Failed queries for non-existent or misconfigured domains
Because DNS happens before most connections are established, it is often an early signal of both legitimate activity and abuse.
How DNS queries are measured
DNS queries are typically measured at the resolver or network level. Common measurement methods include:
Query count
This is the total number of DNS requests observed over a period of time. It is often measured per second, minute, or day.
High query volumes may indicate:
- Popular services or applications
- Misconfigured clients repeatedly retrying
- Malware or automated abuse
Unique queries
This measures how many distinct domains or subdomains are queried.
A high number of unique domains in a short time can signal:
- Domain generation algorithms
- Phishing or scam campaigns
- Bot-driven activity
Query rate
Query rate tracks how quickly DNS requests arrive.
Sudden spikes in query rate may point to:
Response codes
DNS responses include status codes such as NOERROR, NXDOMAIN, or SERVFAIL.
Large volumes of failed lookups often indicate:
- Typo-squatting attempts
- Malicious infrastructure probing
- Poorly configured applications
Source distribution
Measuring where queries come from helps identify:
- Concentrated abuse from specific IP ranges
- Regional traffic patterns
- Compromised hosts inside a network
Why DNS measurement matters for security
DNS is one of the earliest places where malicious behavior appears.
Phishing campaigns often generate DNS queries before emails are delivered. Malware frequently checks in with command-and-control domains using DNS. Scam infrastructure tends to rely on newly registered domains that show unusual lookup patterns.
By measuring DNS queries, security teams gain:
- Earlier detection of emerging threats
- Better visibility into network abuse
- Data to support faster response decisions
DNS measurement challenges
Despite its value, DNS data comes with challenges:
- Volume: Large networks process millions or billions of queries per day
- Noise: Legitimate traffic and abuse often look similar at first glance
- Privacy: DNS data must be handled carefully to respect user privacy
- Correlation: DNS alone is powerful, but stronger when combined with other signals
Automation and enrichment are key to turning raw DNS logs into usable intelligence.
Where DNS fits into network abuse detection
DNS data plays a critical role in identifying:
- Newly observed malicious domains
- Fast-flux hosting patterns
- Infrastructure reused across campaigns
- Early-stage phishing and malware activity
When combined with other telemetry, DNS helps map where abuse lives on the internet.
This infrastructure-focused view aligns closely with how modern threat intelligence platforms, including those used by Abusix, approach abuse detection and remediation.
Common misconceptions about DNS queries
- “DNS is just for name resolution.”
In reality, DNS is a major visibility layer for security and operations.
- “Only enterprises need DNS analytics.”
ISPs, hosting providers, and cloud platforms benefit the most because they see abuse at scale.
- “Blocking domains is enough.”
Blocking without understanding query behavior often leads to false positives and missed threats.
DNS queries are small signals with big impact
DNS queries are simple by design, but at scale they tell powerful stories about how the internet is being used and abused. Measuring them correctly helps networks improve performance, protect users, and reduce the lifespan of malicious infrastructure.
If you want to better understand how DNS data fits into broader network abuse detection and reporting, visit https://www.abusix.com/contact-us and continue the conversation.
FAQ
What is a DNS query in simple terms?
A DNS query is a request that translates a domain name into information like an IP address so devices know where to connect.
How many DNS queries does a network usually see?
It depends on size. Large ISPs and cloud providers often handle millions to billions of DNS queries per day.
Are DNS queries encrypted?
Some are. Protocols like DoH and DoT encrypt DNS queries, but measurement is still possible at resolver and infrastructure levels.



