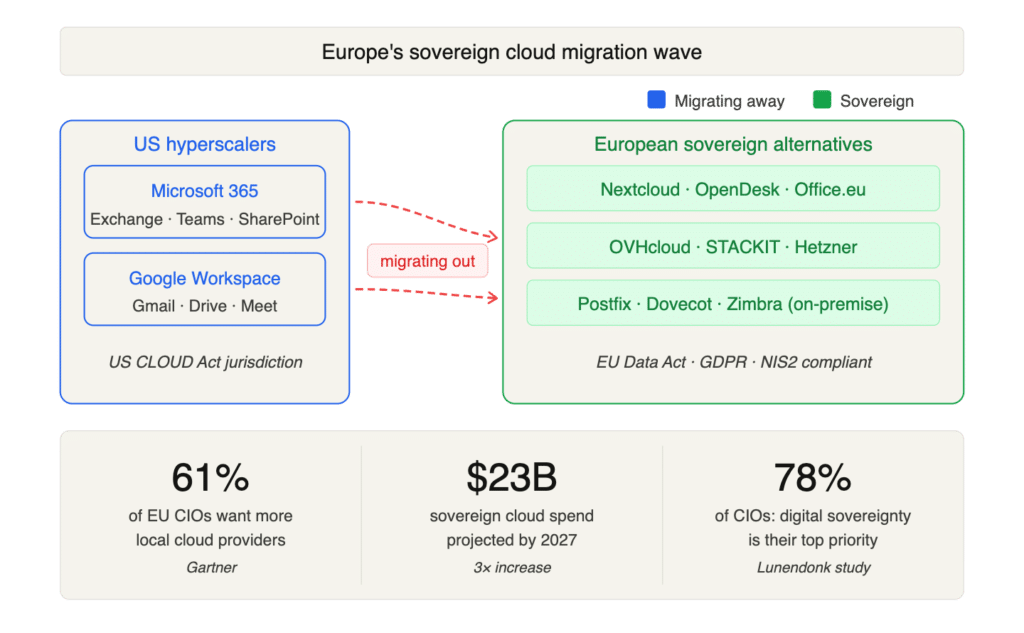
Something remarkable is happening across Europe’s IT landscape. Governments, enterprises, and public institutions are actively migrating their email and collaboration systems away from US hyperscalers, and the pace is accelerating fast.
Germany’s state of Schleswig-Holstein is moving 25,000 government employees off Microsoft 365 and onto open-source alternatives. Denmark’s federal government is stepping away from Microsoft software entirely. France is replacing US-based collaboration tools across government agencies and has launched its own domestic alternative to Microsoft Teams. The International Criminal Court in The Hague switched to the European open-source suite OpenDesk after its chief prosecutor was reportedly locked out of his Microsoft Outlook account following US sanctions. And in December 2025, Airbus announced a 50 million euro, ten-year migration of mission-critical systems away from Google and Microsoft to a sovereign European cloud platform.
These aren’t isolated incidents. According to Gartner, 61% of European CIOs and tech leaders want to increase their use of local cloud providers, and more than half say geopolitics will prevent them from leaning further into US-based hyperscalers. Sovereign cloud spending in Europe is projected to more than triple to $23 billion by 2027. A Lunendonk study found that digital sovereignty has become the top priority for 78% of surveyed CIOs.
The driving forces behind this shift are clear: the US CLOUD Act, which allows American authorities to demand data from US-controlled providers regardless of where servers are located; the full applicability of the EU Data Act since September 2025, which grants data portability rights; GDPR enforcement that has moved beyond high-profile fines to actively scrutinising everyday data transfers; and a volatile geopolitical climate where trade tariffs and political tensions have made digital dependency a tangible business risk.
As Airbus EVP Catherine Jestin put it: sensitive information must remain under European control. And in July 2025, Microsoft’s own legal representative confirmed in a French court that the company cannot guarantee immunity from the CLOUD Act. For European organisations, the message is unmistakable.
Where They’re Going
The migration paths vary. Some organisations are moving to European-born SaaS platforms like Nextcloud (which reports more than triple demand since early 2025), the newly launched Office.eu (a fully European-owned Microsoft 365 alternative operating from The Hague since March 2026), or sovereign cloud providers like OVHcloud, Open Telekom Cloud, STACKIT, and Hetzner.
Others, particularly those in regulated industries, defence, and government, are going fully on-premise or private cloud, deploying open-source email stacks built on Postfix, Dovecot, SOGo, or Zimbra, often paired with collaboration suites like OpenDesk or Nextcloud Hub.
The European Digital Infrastructure Consortium for Digital Commons, established by Germany, France, Italy, and the Netherlands in mid-2025, is accelerating joint development of sovereign digital tools. New entrants and mature European providers alike are offering increasingly competitive infrastructure within the EU legal framework.
The ambition is real. The execution is underway. But there’s a problem hiding in plain sight.
The Spam Protection Gap No One Is Talking About
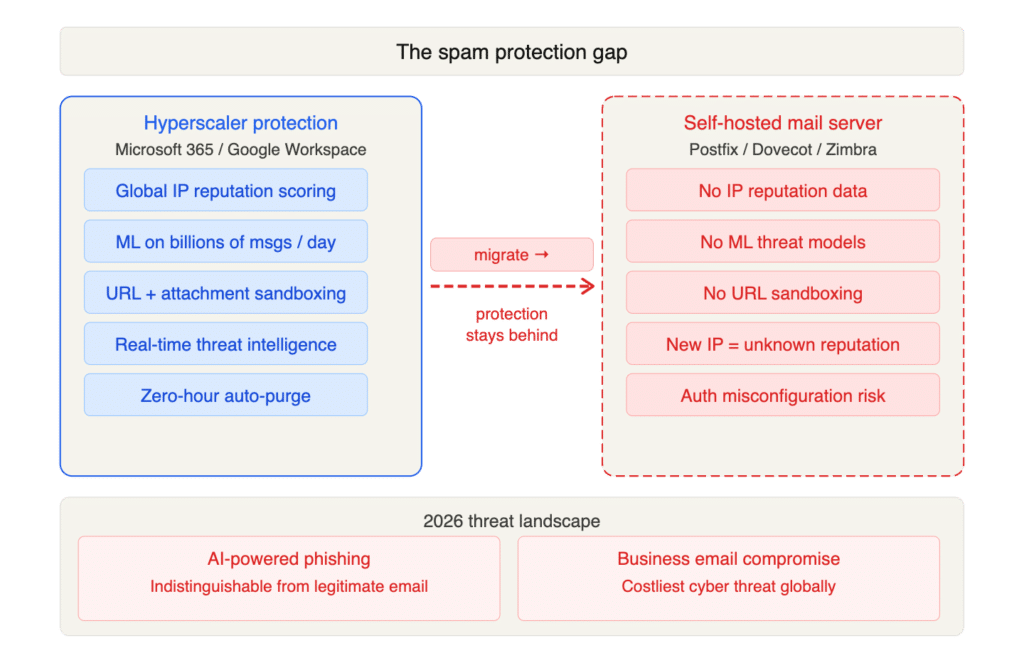
Here’s what most discussions about digital sovereignty overlook: when you leave Microsoft 365 or Google Workspace, you don’t just lose your email client and calendar. You lose one of the most sophisticated spam, phishing, and malware filtering ecosystems ever built.
Microsoft and Google process billions of messages per day. Their anti-spam systems are powered by global-scale threat intelligence, machine learning models trained on enormous datasets, real-time reputation scoring, and continuous feedback loops from hundreds of millions of users. Microsoft Defender for Office 365 alone combines connection filtering, content analysis, URL scanning, sandboxing, and zero-hour auto purge across a vast infrastructure.
When an organisation migrates to an on-premise Postfix server, a self-hosted Nextcloud Mail instance, or a smaller European email provider, that blanket of protection doesn’t follow. And the timing couldn’t be worse. The email threat landscape in 2026 is more dangerous than ever:
- AI-powered phishing has made social engineering attacks nearly indistinguishable from legitimate business communication
- Phishing kits are available for under $25, giving even low-skilled attackers the tools to steal credentials and deploy malware
- Stricter authentication standards (SPF, DKIM, DMARC) have raised the complexity bar, and misconfiguration during migration can actually increase vulnerability
- Business email compromise (BEC) remains one of the costliest cyber threats globally
Migrating email infrastructure is a 6-to-18-month undertaking. During and after that transition, organisations are particularly exposed. DNS changes, new IP reputations, reconfigured authentication records, and unfamiliar filtering tools create windows of vulnerability that sophisticated threat actors are only too happy to exploit.
Sovereignty Without Security Is an Illusion
Digital sovereignty rests on three pillars: security, resilience, and freedom of choice. Moving your email to a European provider or on-premise infrastructure addresses resilience and freedom of choice, but it can actually weaken the security pillar if you don’t replace the threat protection you left behind.
A self-hosted email server without enterprise-grade spam filtering is like a fortress with no guards at the gate. You control the walls, but anything can walk through the front door.
This is the challenge that European IT leaders now face: how do you achieve genuine digital sovereignty for email without sacrificing the spam and threat protection your users have come to rely on?
The Answer Is Already Built Into Your Mail Server
The good news is that achieving sovereignty doesn’t mean starting from scratch on spam protection. Open-source mail servers like Postfix, Exim, or Zimbra are battle-tested and highly capable. What they need is the right threat intelligence feeding into them.
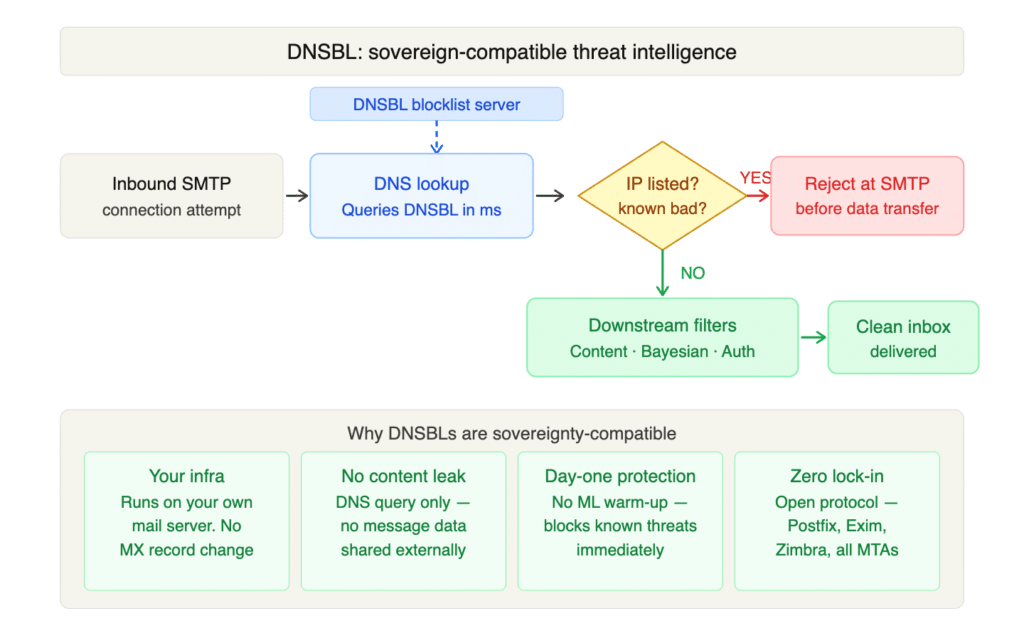
This is where DNS-based blocklists (DNSBLs) come in, and why they deserve far more attention in the sovereignty conversation than they’re currently getting.
When a mail server receives an inbound connection, the very first question it should ask, before accepting a single byte of message data, is: can this sender be trusted? A DNSBL answers that question. A simple, lightweight DNS query tells the mail server in milliseconds whether the connecting IP or domain is a known source of spam, phishing, or malware.
This is the same fundamental mechanism that powers spam filtering at the hyperscaler level. Microsoft, Google, and Yahoo all rely heavily on IP and domain reputation data to make their filtering decisions. The difference is that inside Microsoft 365 or Google Workspace, that reputation data was bundled invisibly into a proprietary platform you didn’t control. With a dedicated blocklist, that intelligence becomes yours to deploy, on your own infrastructure, under your own rules, with full sovereignty intact.
Why DNSBLs Are Built for the Sovereignty Migration
They run entirely on your infrastructure. Your mail server queries the blocklist via standard DNS lookups. No email content is shared with a third party. No MX record changes required. No appliance to install. It’s fully compatible with the sovereignty model these organisations are building.
They work with every major MTA. Postfix, Exim, Zimbra, any mail transfer agent that supports DNSBL lookups. Integration is a configuration change, not a project. You get professional-grade threat intelligence plugged directly into the tools you already manage.
They provide protection from day one. Configuring a blocklist is one of the first things you can do when standing up a new mail server. There’s no waiting for machine learning models to "learn" your traffic patterns. The server starts rejecting known-bad senders immediately.
They dramatically reduce load on downstream filters. By blocking connections from known-bad sources at the SMTP level, before message content is even transferred, you reduce the volume of mail that content filters, Bayesian analysis, and authentication checks need to process. This makes the entire filtering stack faster and more accurate.
They carry zero vendor lock-in. DNSBL is a standard, open protocol. You can layer multiple blocklists, swap providers, or combine them with other filtering tools at will. There’s no proprietary integration, no agent, no dependency. It’s sovereignty-friendly by design.
Making the Move With Confidence
The European email migration isn’t a question of "if" anymore. Regulatory pressure from the EU Data Act, GDPR, NIS2, and DORA is converging with geopolitical reality to make this shift inevitable. For many organisations, 2026 is the year the planning turns into execution.
But sovereignty without security is incomplete. The organisations that get this right are the ones that think about threat intelligence before they flip the MX records, not after the first phishing wave hits an unprotected inbox.
Adding a high-quality blocklist to your new mail server is one of the simplest, most impactful steps you can take. It’s the first line of defence that the hyperscalers built their entire filtering empires on top of, and it’s the one piece of that stack you can replicate on your own terms, on your own infrastructure, on day one.
Your email deserves to be sovereign. A good blocklist makes sure it’s safe, too.



