Most security teams agree they need threat intelligence. Fewer agree on what “good” threat intelligence actually looks like.
The market is crowded with feeds, platforms, reports, and dashboards, all promising better detection and faster response. Some deliver real value. Others add noise, cost, and confusion.
This guide is for buyers who want clarity. We will break down what threat intelligence is, how to evaluate it, and how to avoid the most common mistakes.
What threat intelligence actually is
Threat intelligence is curated, contextual information about malicious activity that helps organizations prevent, detect, and respond to threats.
Good threat intelligence answers questions like:
- Who is attacking?
- What infrastructure is being used?
- Where is the activity coming from?
- How is it changing over time?
- What action should be taken?
Bad threat intelligence answers none of those questions clearly.
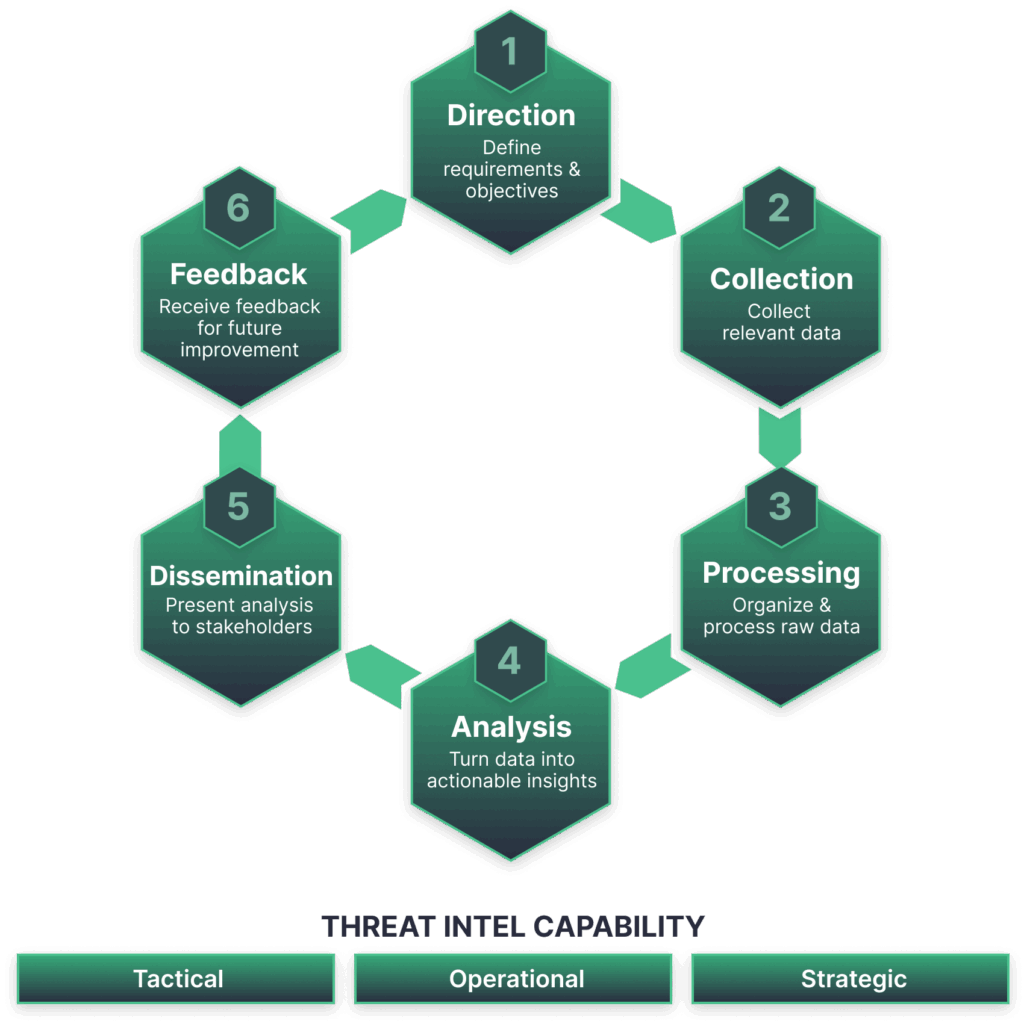
The main types of threat intelligence
Strategic threat intelligence
This is high-level insight meant for leadership and risk teams. It focuses on trends, motivations, and long-term risk.
It is useful for planning, but rarely actionable on its own.
Tactical threat intelligence
This includes indicators such as IP addresses, domains, and URLs. It is commonly used in detection systems.
Tactical intel is easy to consume but expires quickly.
Operational threat intelligence
This type connects tactics to real-world campaigns. It helps teams understand how attacks unfold and how infrastructure is reused.
Operational intel is valuable for investigations and response.
Infrastructure-focused threat intelligence
This focuses on where abuse lives on the internet: IP ranges, networks, ASNs, and hosting environments.
It is especially valuable for ISPs, hosting providers, and teams responsible for large-scale networks.
What buyers should evaluate first
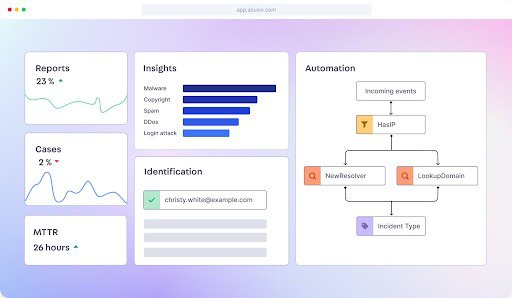
Actionability
If intelligence does not lead to a decision or an action, it is just data.
Ask:
- Does this feed tell us what to block, investigate, or report?
- Can it trigger workflows automatically?
- Does it reduce response time?
Timeliness
Threat intelligence loses value fast.
Look for:
- Real-time or near real-time updates
- Clear visibility into when data was first observed
- Low lag between detection and delivery
Old indicators create false confidence.
Coverage and perspective
Many feeds focus narrowly on domains or malware samples. That leaves blind spots.
Stronger intelligence combines:
- Network-level signals
- Behavioral patterns
- Multiple attack vectors
Infrastructure-focused visibility is often missing and increasingly important.
Accuracy and validation
False positives cost time and credibility.
Buyers should ask:
- How is data validated?
- Is there correlation across multiple sources?
- Are confidence levels provided?
More data does not mean better data.
Integration matters more than features
Threat intelligence that lives in a portal rarely gets used.
Buyers should prioritize:
If intelligence cannot flow into existing tools, adoption will suffer.
How threat intelligence supports security frameworks
Many buyers need to justify threat intelligence in terms of standards and audits.
Threat intelligence aligns well with frameworks such as the NIST Cybersecurity Framework, particularly the Identify and Detect functions.
It also supports requirements under:
- ISO 27001 for risk assessment and monitoring
- NIS2 for detection and response readiness
The key is being able to show how intelligence informs action.
Common buying mistakes to avoid
Buying too many feeds
More feeds often mean more noise. Correlation becomes harder, not easier.
Quality and coverage matter more than volume.
Confusing reports with intelligence
Beautiful reports are useful for awareness, not defense.
If intelligence cannot be operationalized, it will be ignored during real incidents.
Ignoring infrastructure-level visibility
Attackers rely on networks and hosting to operate. Intelligence that ignores infrastructure misses repeat abuse patterns.
This gap is especially costly for providers and large platforms.
Treating threat intelligence as a standalone tool
Threat intelligence works best when paired with automation, reporting, and remediation workflows.
On its own, it becomes another dashboard no one checks.
Questions every buyer should ask vendors
Before signing anything, ask:
- Where does your data come from?
- How quickly is new intelligence delivered?
- How do you reduce false positives?
- What actions can this intelligence drive?
- How does this integrate with our existing stack?
- What visibility do we get into abuse at the network level?
Clear answers usually separate mature providers from marketing-heavy ones.
Where Guardian Intel fits in
Guardian Intel focuses on infrastructure-focused threat intelligence. Instead of only tracking domains or malware, it maps malicious activity across IPs, networks, and regions in near real time.
This approach is especially useful for:
- ISPs and hosting providers
- Abuse and trust teams
- SOCs dealing with large-scale, repeat abuse
It helps close the gap between detection and takedown by showing where threats originate, not just what they look like.
Threat intelligence should make security simpler
The right threat intelligence reduces uncertainty. It shortens response time, improves confidence, and helps teams focus on real risk.
The wrong intelligence adds noise and drains resources.
A careful buying process, grounded in actionability and integration, makes all the difference.
If you are evaluating threat intelligence and want a clearer view of abuse at the infrastructure layer, visit https://www.abusix.com/contact-us to continue the conversation.
FAQ
What is the biggest benefit of threat intelligence?
It helps organizations detect and respond to threats faster by providing external context they cannot generate internally.
Is free threat intelligence good enough?
Free feeds can help, but they often lack validation, timeliness, and support needed for operational use.
Who should own threat intelligence internally?
Typically SOC, security operations, or abuse teams, with input from risk and compliance.
How often should threat intelligence be updated?
Ideally in real time or near real time. Stale data loses value quickly.
Can threat intelligence reduce false positives?
Yes. High-quality intelligence improves confidence and reduces unnecessary investigations.