Most security conversations focus on content. What is inside the email. What the payload looks like. What the URL does.
But long before content is inspected, decisions are already being made. Those decisions are based on IP reputation.
If your IP has a bad reputation, traffic gets blocked, delayed, or scrutinized heavily. If your reputation is good, traffic flows. That makes IP reputation one of the most important and least visible control points on the internet.
What IP reputation actually is
IP reputation is a trust score built from observed behavior over time. It reflects how an IP address or network behaves, not what it claims to be.
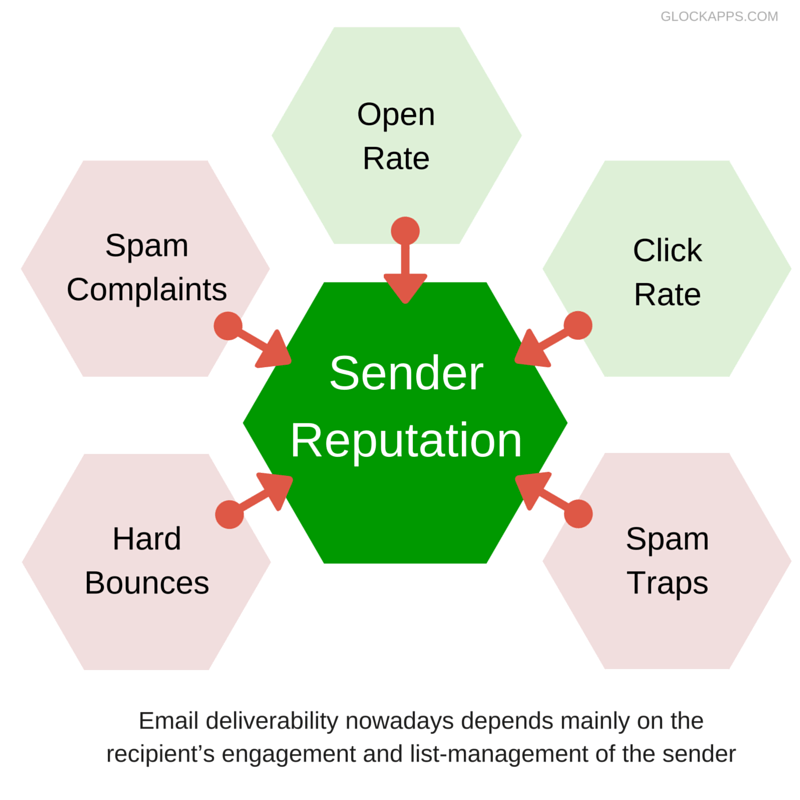
Reputation systems look at patterns such as:
- Volume and consistency of traffic
- Spam and phishing indicators
- Malware or abuse reports
- Historical behavior across networks
In simple terms, IP reputation answers one question:
Should this connection be trusted?
Why IP reputation matters more than people realize
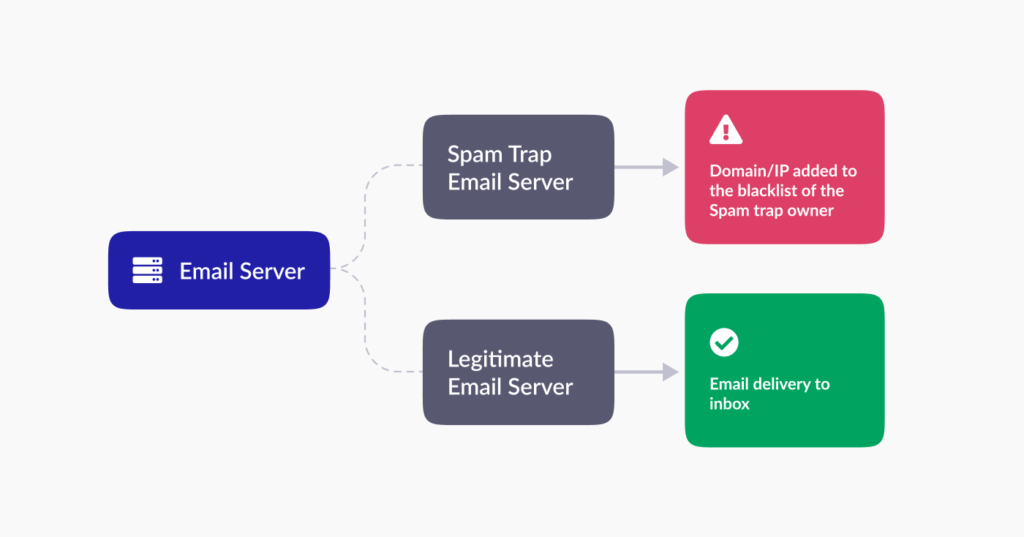
It determines email delivery before filters run
Mail platforms make early decisions based on IP reputation. A poor score can mean:
No subject line or content tweak can fix a reputation problem.
It affects more than email
Email is just the most visible example.
IP reputation also influences:
- API access
- Web application firewalls
- Rate limiting
- DDoS mitigation responses
A bad reputation increases friction everywhere your IP shows up.
It compounds across shared infrastructure
In hosting and cloud environments, one abusive tenant can affect others.
When multiple customers share IP space, reputation becomes a shared responsibility. Unchecked abuse can poison an entire range and impact innocent users.
How IP reputation is built, or broken
IP reputation is not static. It changes constantly based on behavior.
Positive signals include:
- Consistent, legitimate traffic patterns
- Clean outbound email behavior
- Fast response to abuse reports
Negative signals include:
- Spam or phishing activity
- Compromised accounts sending bulk mail
- Malware hosting or command-and-control traffic
- Ignored abuse complaints
Once negative signals stack up, recovery gets harder and slower.
Where IP reputation causes real damage
Deliverability failures that look mysterious
Many teams chase deliverability problems by adjusting filters or content, while the real issue sits upstream at the IP level.
If the reputation is damaged, nothing downstream fixes it.
Customer trust erosion
When emails fail or services get blocked, customers blame the provider, not the reputation system.
For ISPs and hosting providers, repeated reputation issues translate into:
- Support tickets
- Churn
- Brand damage
Regulatory and compliance pressure
Poor reputation often signals unresolved abuse. Regulators increasingly expect providers to act on known malicious activity.
Ignoring reputation problems can look like negligence rather than technical failure.
Why reputation is an infrastructure problem
Reputation is earned or lost at the infrastructure layer.
Most large-scale abuse originates from ISP, cloud, or hosting subscriber networks. If abuse is not detected and addressed at the source, reputation damage spreads quickly.
That is why reputation management is not just a mail admin task. It is a network responsibility.
How reputation systems actually make decisions
Reputation engines do not rely on a single event. They correlate many signals over time, often across multiple data sources.
Commercial reputation providers such as Spamhaus and Abusix invest heavily in:
- Global telemetry
- Abuse correlation
- False positive reduction
- Transparent delisting processes
This correlation is what makes reputation harder to game than content-based filters.
The role of IP reputation in layered defense
Strong security stacks use IP reputation as an early control.
A typical flow looks like this:
- IP reputation check at connection time
- Policy and protocol validation
- Content and behavioral analysis
- Post-delivery monitoring
Stopping bad traffic early reduces cost and risk downstream.
Common mistakes that destroy reputation
- Ignoring outbound abuse
- Letting compromised accounts run unchecked
- Treating abuse reports as low priority
- Relying on reactive cleanup instead of prevention
Each mistake signals to reputation systems that a network is not under control.

How to protect and improve IP reputation
Effective reputation management requires consistency.
Key steps include:
- Monitoring outbound traffic continuously
- Acting quickly on abuse signals
- Automating abuse handling where possible
- Reporting and resolving issues at the source
- Using high-quality reputation data at the connection layer
Reputation improves when abuse stops staying alive.
Why IP reputation is a business issue, not just a technical one
IP reputation affects revenue, customer experience, and operational cost. It determines whether traffic is trusted or treated with suspicion before anyone reads a single byte.
For mail platforms, hosting providers, and ISPs, reputation is one of the clearest signals the internet uses to judge reliability.
If you want better visibility into how reputation is formed and how abuse impacts it at the network level, visit https://www.abusix.com/contact-us to learn more.
FAQ
What is IP reputation in simple terms?
It is a trust score based on how an IP behaves over time, used to decide whether traffic should be accepted or blocked.
How fast can IP reputation change?
Very fast. New abuse can damage reputation in hours. Recovery often takes much longer.
Does IP reputation only affect email?
No. It also affects web access, APIs, and security controls across the internet.
Can one bad customer ruin a shared IP?
Yes. Shared infrastructure means shared reputation if abuse is not contained.
How do you recover a bad IP reputation?
By stopping abuse, responding to reports quickly, and maintaining clean behavior consistently over time.



