When people hear “network abuse,” they often think of spam. That view is outdated. Today’s abuse ecosystem is far more complex, faster moving, and harder to contain.
Modern attacks blend phishing, malware, botnets, and infrastructure misuse across hosting providers, cloud platforms, and ISPs. If abuse is not addressed at the network level, it spreads quietly and scales fast. That is why understanding the different forms of network abuse is the first step toward stopping it.
What network abuse really means
Network abuse is any malicious or unauthorized use of internet infrastructure that causes harm to users, services, or other networks.
A few simple examples:
- A compromised server sending phishing emails
- A hijacked virtual machine launching DDoS attacks
- An abused hosting account distributing malware
- Infrastructure used to host scam landing pages
The common thread is infrastructure. Abuse almost always relies on legitimate networks being misused.

The most common faces of network abuse
Spam and bulk email abuse
Spam is still the most visible form of abuse, but it has evolved. Today’s spam often acts as a delivery mechanism for phishing, malware, and fraud rather than just unwanted ads.
Abused mail servers and compromised accounts can damage entire IP ranges, not just a single sender.
Phishing infrastructure
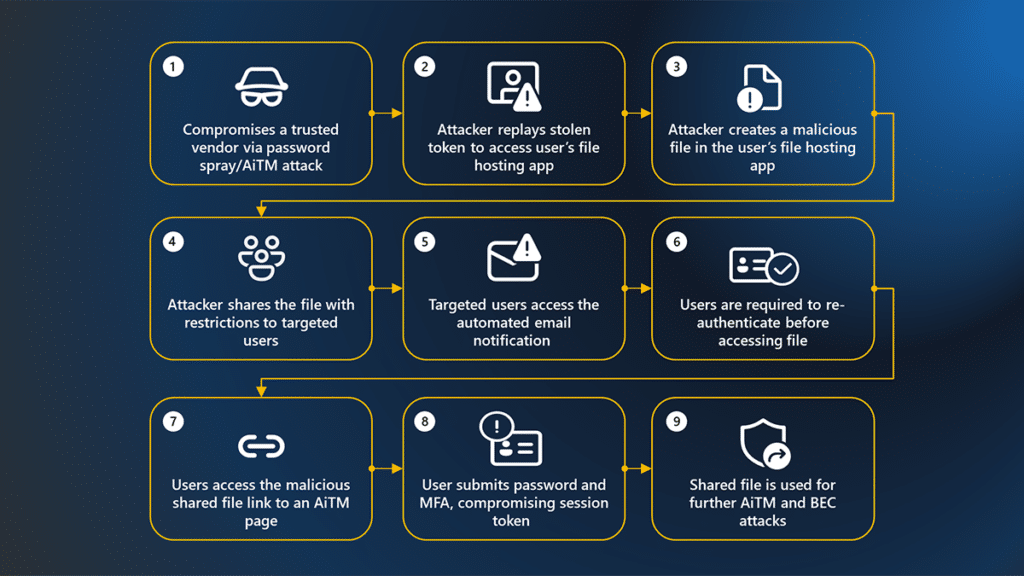
Phishing is no longer just about emails. Attackers spin up fast, disposable hosting to run fake login pages, brand impersonation sites, and credential harvesters.
These sites often live for hours, not days, which makes fast detection and takedown critical.
Malware distribution and command-and-control
Many networks unknowingly host malware loaders or command-and-control infrastructure. Once active, these systems manage infected devices, steal data, or launch secondary attacks.
Even small hosting footprints can cause large downstream damage.
Botnets and automated abuse
Botnets turn thousands of compromised devices into a single attack platform. They generate spam, scrape content, brute-force logins, and flood networks with traffic.
Because botnets rotate IPs and hosts constantly, slow response allows them to persist.
DDoS staging and amplification
Some abuse does not target victims directly. Instead, networks are used as launch points or amplifiers for distributed denial-of-service attacks.
Misconfigured services, open resolvers, and exposed systems all play a role.
Scam and fraud hosting
Investment scams, fake stores, and impersonation pages rely on short-lived hosting. Abuse reports often pile up while scammers move on to the next server.
Without fast reporting and remediation, this cycle never slows down.
Why network abuse keeps spreading
Abuse lives upstream
More than 98 percent of large-scale abuse originates from ISP, cloud, or hosting subscriber networks. Endpoint security alone cannot fix that.
If the infrastructure stays online, attackers simply reuse it.
Reporting is fragmented
Many organizations block attacks locally but never report them back to the source network. That leaves the underlying problem untouched.
Manual abuse handling does not scale
Abuse desks are overwhelmed. Reports arrive in different formats, with varying quality, and often too late to matter.
Automation gaps give attackers time to adapt.
Reputation damage compounds
Once a network earns a bad reputation, even clean customers suffer. Deliverability drops, trust erodes, and support costs rise.
Where network abuse causes the most harm
Network abuse does not stay contained. It leads to:
- Compromised users and stolen credentials
- Financial fraud and scams
- Blacklisted IP ranges and domains
- Increased operational costs
- Regulatory and compliance pressure
For hosting providers and ISPs, abuse is no longer just a technical issue. It is a business risk.
A defense-in-depth approach to network abuse
Effective mitigation requires multiple layers working together.
- Early detection using threat intelligence and telemetry
- Validation to reduce false positives and noise
- Rapid reporting back to originating networks
- Automated response to shorten time to takedown
- Feedback loops to improve future detection
Stopping abuse at the source reduces harm everywhere else.
Tools that help close the gap
Modern abuse management platforms are designed for this reality.
Solutions like Abusix Guardian Ops help hosting providers and ISPs automate abuse intake, correlate events, and act quickly. By combining reporting, remediation, and visibility, teams can move from reactive cleanup to proactive prevention.
Threat intelligence services such as Abusix Guardian Intel also provide real-time insight into where abuse lives across IPs, networks, and regions.
Common mistakes that keep abuse alive
- Treating abuse as a ticketing problem instead of a network problem
- Blocking locally without reporting upstream
- Relying on manual review for high-volume abuse
- Ignoring reputation signals until damage is done
Each of these mistakes extends the life of abuse campaigns.
Network abuse is an infrastructure problem
The many faces of network abuse all point to the same conclusion. Attacks succeed because infrastructure allows them to persist.
Cleaning up the internet requires cooperation between victims, hosting providers, and origin networks. When abuse is detected, reported, and resolved quickly, everyone benefits.
If you want to understand how network-level reporting and automation fit into your environment, visit https://www.abusix.com/contact-us and start the conversation.
FAQ
What is network abuse in simple terms?
Network abuse is the misuse of internet infrastructure to send spam, run scams, distribute malware, or launch attacks.
Why do hosting providers play such a big role?
Most abuse relies on hosting, cloud, or ISP infrastructure. Providers control the systems attackers depend on.
Is spam still considered network abuse?
Yes, but spam today often acts as a delivery channel for phishing, malware, and fraud rather than being the end goal.
Why is reporting abuse back to the source important?
Reporting enables the originating network to shut down abusive systems, preventing repeat attacks and broader spread.
Can automation really reduce abuse?
Yes. Automation shortens response time, reduces analyst workload, and limits how long attackers can operate.



